BF Specification of CVE-2014-0160 Heartbleed Heap Buffer Over-Read in OpenSSL v1.0.1 before v1.0.1g
-0.png)
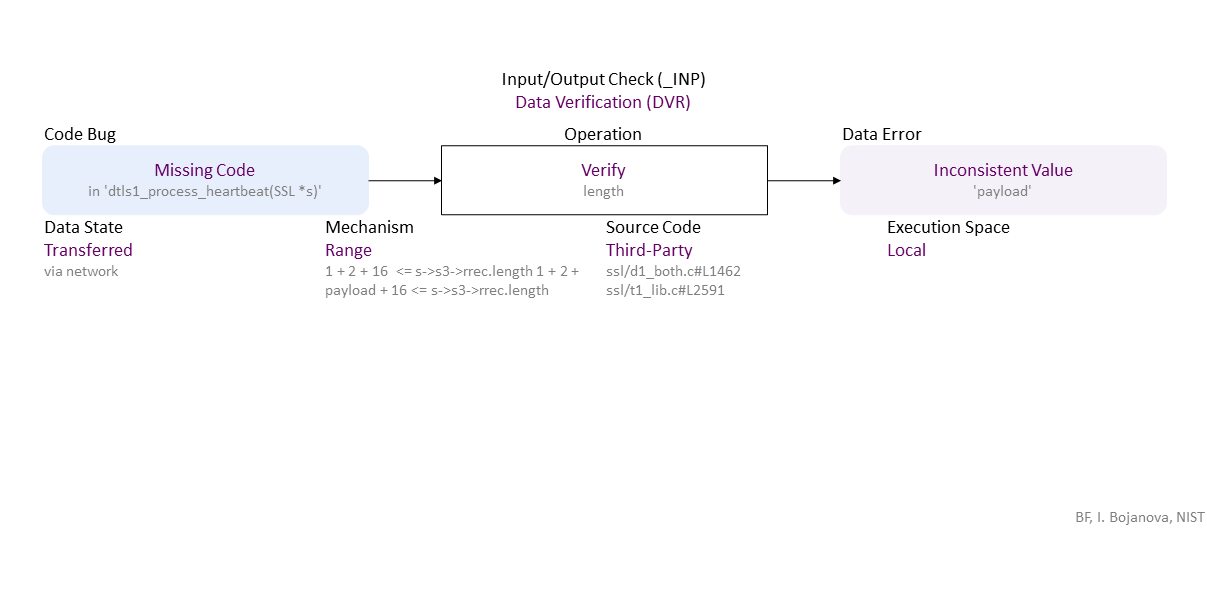
//generated// Missing Code (in ‘dtls1_process_heartbeat(SSL *s)’) to Range Verify length (1 + 2 + 16 <= s->s3->rrec.length 1 + 2 + payload + 16 <= s->s3->rrec.length) Transferred (via network) in Third-Party (ssl/d1_both.c#L1462 ssl/t1_lib.c#L2591) Local leads to Inconsistent Value (‘payload’)
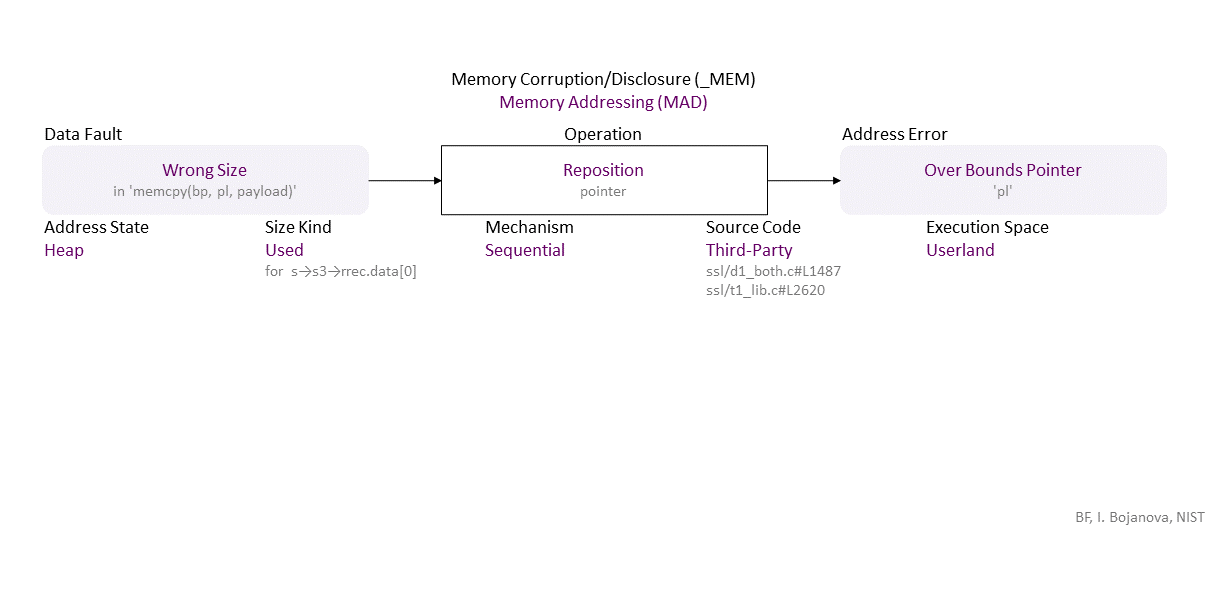
, which propagates to Wrong Size (in ‘memcpy(bp, pl, payload)’) Sequential Reposition (pointer) Heap Used (for s→s3→rrec.data[0]) Third-Party (ssl/d1_both.c#L1487 ssl/t1_lib.c#L2620) in Userland that results in Overbound Pointer (‘pl’)
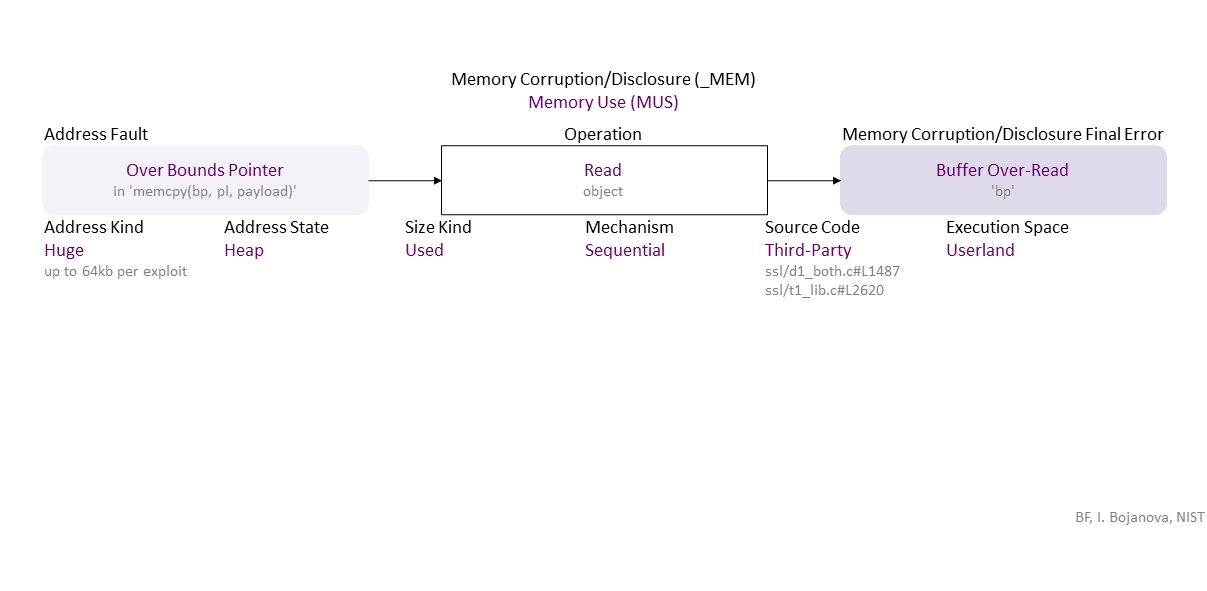
, which propagates to Overbound Pointer (in ‘memcpy(bp, pl, payload)’) Sequential Read (object) Used Huge (up to 64kb per exploit) Heap Third-Party (ssl/d1_both.c#L1487 ssl/t1_lib.c#L2620) in Userland that results in Buffer Over-Read (‘bp’)
, which can be exploited toward IEX (confidentiality loss) security failure.
|
| Class | Definition |
| DVR | Data Verification (DVR) class – Data are verified (i.e., semantics check) or corrected (i.e., assign or remove) improperly. |
| MAD | Memory Addressing (MAD) class – The pointer to an object is initialized, dereferenced, repositioned, or reassigned to an improper memory address. |
| MUS | Memory Use (MUS) class – An object is initialized, read, written, or cleared improperly. |
| Operation | Definition |
| Verify | Verify operation – Check data semantics (e.g., proper value/meaning) in order to accept (and possibly correct) or reject it. |
| Reposition | Reposition operation – Change the pointer to another position inside its object. |
| Read | Read operation – Retrieve the data value of an object from memory. |
| Cause/Consequence | Definition |
| Code Bug | Code Bug type – An error in the implementation of an operation – proper operands over an improper operation. A first cause for the chain of weaknesses underlying a software security vulnerability. Must be fixed to resolve the vulnerability. |
| Missing Code | Missing Code bug - The operation is entirely absent. |
| Data Error/Fault | Data Fault/Error type – The data of an object has harmed semantics or inconsistent or wrong value. |
| Inconsistent Value | Inconsistent Value fault/error – The data value does not correspond to related data value (e.g., inconstancy between the value of a size variable and the actual buffer size). |
| Wrong Size | Wrong Size fault/error – The value used as size or length (i.e., the number of elements) does not match an object's memory size or length (e.g., to limit a pointer reposition or index increment/decrement in a repetition statement). |
| Address Error/Fault | Address Fault/Error type – The address of an object is wrong. |
| Overbound Pointer | Overbound Pointer fault/error – Holds an address that is above the upper boundary of its object. |
| Memory Corruption/Disclosure Final Error | Memory Corruption/Disclosure final error type – An exploitable or undefined system behavior caused by memory addressing, allocation, use, or deallocation bugs. |
| Buffer Over-Read | Buffer Over-Read final error – Read data above the upper bound of an object. |
| Operation Attribute | Definition |
| Mechanism | Mechanism operation attribute type – Shows how the operation the operation with a bug or faulty operand is performed. |
| Range | Range operation attribute – The operation checks data are within a (min, max) interval. |
| Sequential | Sequential operation attribute – The operation is via iterating over the object elements. |
| Source Code | Source Code operation attribute type – Shows where the code of the operation with a bug or faulty operand resides within the software, firmware, or hardware. |
| Third-Party | Third-Party operation attribute – The operation code is in a third-party source. |
| Execution Space | Execution Space operation attribute type – Shows where the operation with a bug or faulty operand is executed and the privilege level at which it runs. |
| Local | Local operation attribute – The bugged code runs in an environment with access control policy with limited (local user) permission. |
| Userland | Userland operation attribute – The bugged code runs in an environment with privilege levels, but in unprivileged mode (e.g., ring 3 in x86 architecture). |
| Operand Attribute | Definition |
| Data State | Data State operand attribute type – Shows where the data comes from. |
| Transferred | Transferred operand attribute – Data are from another device via a network (e.g., connecting analog device or another computer). |
| Address State | Address State operand attribute type – Shows where the address is (i.e., its location) in the memory layout. |
| Heap | |
| Size Kind | Size Kind operand attribute type – Shows what is used as the size or length (i.e., the number of elements) of an object - e.g., as the limit for traversal over the elements. |
| Used | Used operand attribute – A supplied value to be used as the size or length (i.e., the number of elements) of an object. |
| Address Kind | Address Kind operand attribute type - Shows how much memory is accessed (i.e., the span) outside the bounds of an object. |
| Huge |