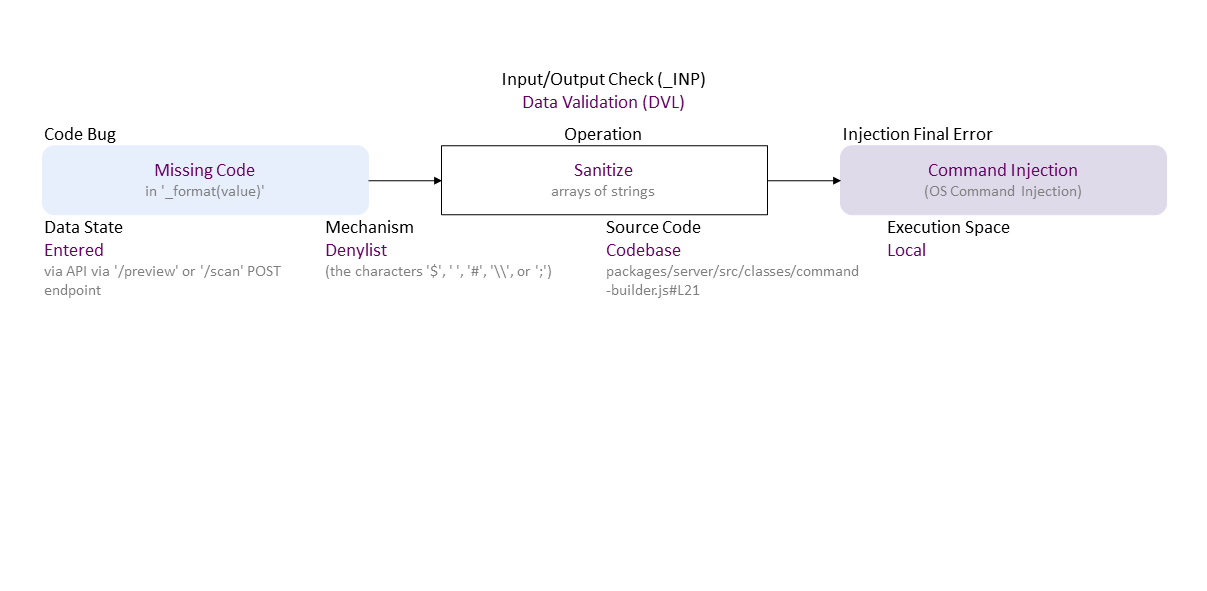
BF Specification of CVE-2023-2564 OS Command Injection in GitHub repository sbs20/scanservjs prior to v2.27.0.
-0.png)
//generated//
Missing Code (in '_format(value)') to Denylist Sanitize arrays of strings ((the characters '$', ' ', '#', '\\', or ';')) Entered (via API via '/preview' or '/scan' POST endpoint) in Codebase (packages/server/src/classes/command-builder.js#L21) Local leads to Command Injection ((OS Command Injection))
. If exploited this can lead to ACE (RCE) (everything could be lost).
|
| Class | Definition |
| DVL | Data Validation (DVL) class – Data are validated (i.e., syntax check) or sanitized (i.e., escape, filter, or repair) improperly. |
| Operation | Definition |
| Sanitize | Sanitize operation – Modify data (e.g., escape/neutralize, filter/remove, or repair/add symbols or elements) to make it valid (well-formed). |
| Cause/Consequence | Definition |
| Code Bug | Code Bug type – An error in the implementation of an operation – proper operands over an improper operation. It is the roor cause of a security vulnerability. Must be fixed to resolve the vulnerability. |
| Missing Code | Missing Code bug - The operation is misplaced entirely absent. |
| Injection Final Error | Injection final error type – An exploitable or undefined system behavior caused by validation or sanitization bugs. |
| Command Injection | Command Injection final error – Maliciously inserted new commands into the input to a command sent to an OS, a server, or an AI model. |
| Operation Attribute | Definition |
| Mechanism | Mechanism operation attribute type – Shows how the operation the operation with a bug or faulty operand is performed. |
| Denylist | Denylist operation attribute – The operation is via a policy based on a set of known bad content; helps reject outright maliciously malformed data. |
| Source Code | Source Code operation attribute type – Shows where the code of the operation with a bug or faulty operand resides within the software, firmware, or hardware. |
| Codebase | Codebase operation attribute – The operation is in the programmer's code - in the application itself. |
| Execution Space | Execution Space operation attribute type – Shows where the operation with a bug or faulty operand is executed and the privilege level at which it runs. |
| Local | Local operation attribute – The bugged code runs in an environment with access control policy with limited (local user) permission. |
| Operand Attribute | Definition |
| Data State | Data State operand attribute type – Shows where the data comes from. |
| Entered | Entered operand attribute – Data are from a user via a user interface (e.g., input field of a dialog or a command prompt). |